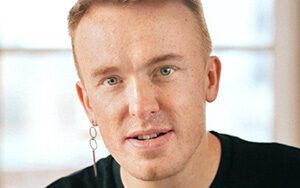
Adam Shostack of Shostack & Associates and author of Threat Modeling: Designing for Security discussed different approaches to threat modeling, the multiple benefits it can provide, and how it can be added to an organization’s existing software process. Host Justin Beyer spoke with Shostack about the steps associated with threat modeling and the different approaches you can take.
Specifically, they discussed methods such as asset centric, threat centric, and software centric approaches to modeling and why software centric is the most beneficial; the purpose of diagramming your applications and introducing Trust Boundaries to those diagrams for the purpose of threat modeling; and different methods to discover threats in your model, such as STRIDE and Kill Chain, and why you might pick certain methods or gamify the process by using the Elevation of Privilege card game. They also discussed different tooling that can be leveraged to develop your model and different approaches you can take to tracking and prioritizing the threats you discover, such as using a Bug Bar and your existing bug tracking system.
The episode also touched on leveraging threat modeling to find privacy threats, using models like LINDDUN, as well as how to sell threat modeling to your organization based on the wide variety of benefits it can provide. Beyer and Shostack ended the episode discussing how threat modeling can be applied to a variety of newer technology models, such as IoT, and how threat modeling is a flexible process that can be adjusted by the user to adapt to these new models.
Show Notes
Related Links
- Berryville Institute of Machine Learning (threat model guide)
- Data flow Diagram (Guest’s Blog)
- Lockheed Martin Kill Chain
- LINDDUN Privacy Model
- SDL Bug Bar
- Threat Dragon
- Continuum
- OWASP “a seat at the table”
- Elevation of privilege card game
- Adam’s blog
- OWASP Threat Modeling Slack Channel
SE Radio theme: “Broken Reality” by Kevin MacLeod (incompetech.com — Licensed under Creative Commons: By Attribution 3.0)